OTP : One-Time Password
One-Time Password (OTP) is a security feature used in authentication systems to verify the identity of a user. It is a temporary code that is typically generated by a computer or mobile device and sent to the user through a secure channel, such as SMS, email, or a dedicated authentication app.
OTPs are used to add an extra layer of security to online accounts and transactions because they are valid for only a short period of time and can only be used once.
How Does OTP Work
- User Request: When a user attempts to log in to an online service or perform a sensitive action (such as making a financial transaction), they are prompted to provide an OTP in addition to their regular username and password.
- Generation: The OTP is generated by a trusted authentication server or device. There are different methods for generating OTPs, including time-based OTPs (TOTPs) and event-based OTPs (HOTPs). TOTPs change after a set period of time (e.g., every 30 seconds), while HOTPs change after each use or event.
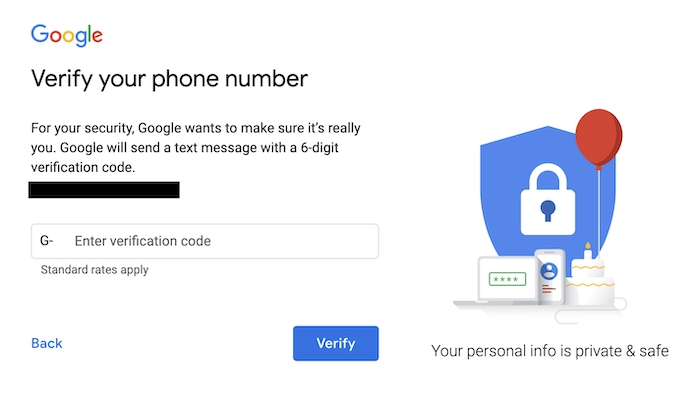
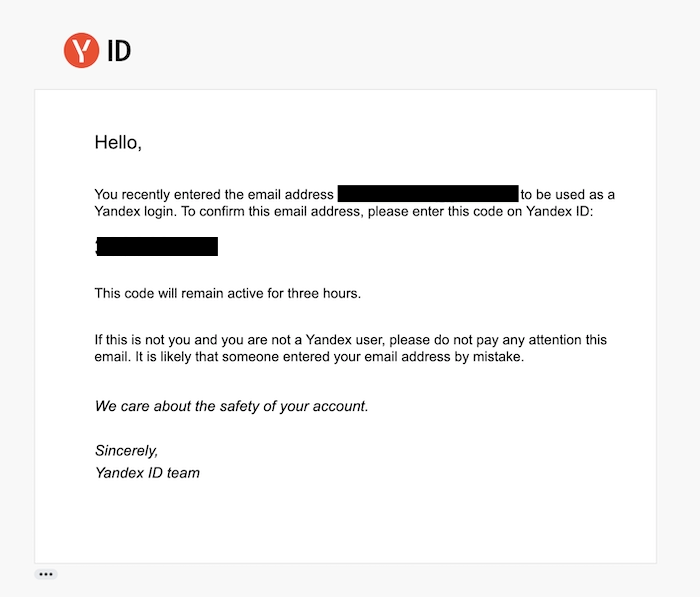
- Delivery: The OTP is delivered to the user through a secure channel. This can be done via SMS, email, or through a dedicated authentication app like Google Authenticator or Authy. The secure delivery ensures that the OTP remains confidential.
- Verification: The user enters the OTP into the login or transaction screen within the time window in which it is valid. The server then verifies the OTP’s correctness.
- Temporary Use: Once used or after a certain period (depending on the type of OTP), the OTP becomes invalid. This means that even if someone intercepts the OTP, they cannot reuse it for unauthorized access.
Why Is OTP Necessary
OTP is a widely used mechanism for two-factor authentication (2FA) and multi-factor authentication (MFA) because it adds an extra layer of security beyond just a password. It helps protect accounts and sensitive information from unauthorized access, phishing attacks, and other security threats.
OTP Types
- Time-Based OTP (TOTP): Time-based OTPs are generated based on a shared secret key and the current time. They typically expire after a short period, such as 30 seconds. Users and the authentication server must be synchronized in terms of time. Popular applications like Google Authenticator and Authy use TOTP for generating OTPs.
- Event-Based OTP (HOTP): Event-based OTPs, also known as HMAC-based OTPs, are generated based on a shared secret key and a counter value that increments with each use. Unlike TOTP, HOTPs do not depend on the current time and can be used without time synchronization between the user and server.
- SMS-Based OTP: In this method, a one-time password is sent to the user’s mobile phone via SMS. The user then enters the OTP to complete the authentication process. While convenient, SMS-based OTPs are considered less secure than other methods because they can be vulnerable to SIM swapping attacks and SMS interception.
Google OTP
- Email-Based OTP: Similar to SMS, an OTP is sent to the user’s email address. The user retrieves the OTP from their email and enters it for authentication. Like SMS, email-based OTPs have some security concerns, especially if the email account itself is compromised.
Yandex Email OTP
- Push Notification OTP: With this method, a push notification is sent to the user’s mobile device through a dedicated authentication app. The user can approve or deny the authentication request with a single tap on their device. This is often more user-friendly than manually entering an OTP.
Google Push Notification OTP

- Hardware OTP Token: Hardware OTP tokens are physical devices that generate OTPs. They are often used in high-security environments. These tokens typically display the OTP on an LCD screen or generate it when a button is pressed. They do not rely on network connectivity, making them resistant to online attacks.
- Biometric OTP: Some systems use biometric data, such as fingerprint scans or facial recognition, to generate or validate OTPs. Biometric OTPs combine biometric authentication with the one-time password concept for enhanced security.
- Grid-Based OTP: In this method, the user is provided with a grid of characters, and they are asked to enter specific characters from the grid as their OTP. The grid can change with each authentication attempt.
- Challenge-Response OTP: This method involves the server sending a challenge to the user, who then responds with an OTP generated based on the challenge and a secret key. The server verifies the response to authenticate the user.